Documentación
- MAGERIT versión 3 (versión español): Metodología de Análisis y Gestión de Riesgos de los Sistemas de Información.- Edita: © Ministerio de Hacienda y Administraciones Públicas, octubre 2012.- NIPO: 630-12-171-8
 Libro I: Método (PDF-1,47 MB)
Libro I: Método (PDF-1,47 MB)
 Libro II: Catálogo de Elementos (PDF-3,37 MB)
Libro II: Catálogo de Elementos (PDF-3,37 MB)
 Libro III: Guía de Técnicas (PDF-1,28 MB)
Libro III: Guía de Técnicas (PDF-1,28 MB)
 Book I: Method (PDF-1,44 MB)
Book I: Method (PDF-1,44 MB) 
 Book I: Method (EPUB-2,94 MB)
Book I: Method (EPUB-2,94 MB)
- MAGERIT V.2 (English version): Methodology for Information Systems Risk Analysis and Management.- Edita: © MAP, junio 2006.- NIPO: 326-06-044-8
 Book I: Method (PDF-1,17 MB)
Book I: Method (PDF-1,17 MB)
 Book II: Catalogue (PDF-270 KB)
Book II: Catalogue (PDF-270 KB)
 Book III: Techniques (PDF-157 KB)
Book III: Techniques (PDF-157 KB)
 Libro I: Metodo (PDF-1,56 MB)
Libro I: Metodo (PDF-1,56 MB)
Introducción
MAGERIT versión 3 es la metodología de análisis y gestión de riesgos elaborada en su día por el antiguo Consejo Superior de Administración Electrónica y actualmente mantenida por la Secretaría General de Administración Digital (Ministerio de Asuntos Económicos y Transformación Digital) con la colaboración del Centro Criptológico Nacional (CCN).
MAGERIT es una metodología de carácter público que puede ser utilizada libremente y no requiere autorización previa. Interesa principalmente a las entidades en el ámbito de aplicación del Esquema Nacional de Seguridad (ENS) para satisfacer el principio de la gestión de la seguridad basada en riesgos, así como el requisito de análisis y gestión de riesgos, considerando la dependencia de las tecnologías de la información para cumplir misiones, prestar servicios y alcanzar los objetivos de la organización.
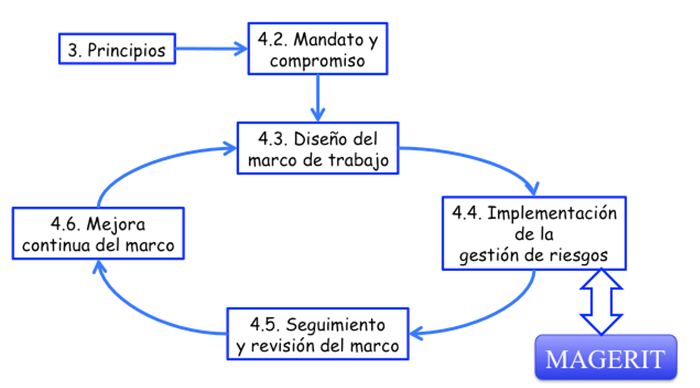
Siguiendo la terminología de la normativa ISO 31000, MAGERIT responde a lo que se denomina “Proceso de Gestión de los Riesgos”, sección 4.4 (“Implementación de la Gestión de los Riesgos”) dentro del “Marco de Gestión de Riesgos”. En otras palabras, MAGERIT implementa el Proceso de Gestión de Riesgos dentro de un marco de trabajo para que los órganos de gobierno tomen decisiones teniendo en cuenta los riesgos derivados del uso de tecnologías de la información.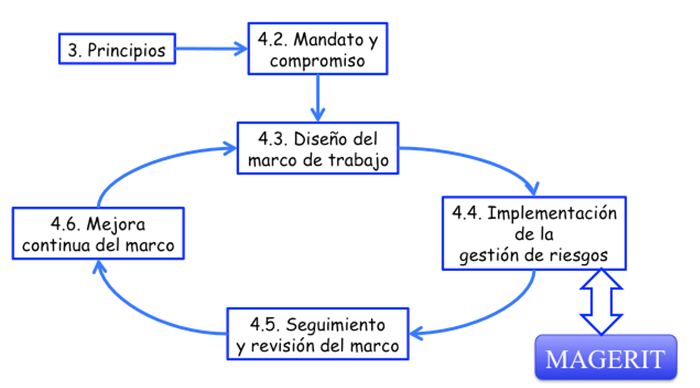
Figura 1. ISO 31000 - Marco de trabajo para la gestión de riesgos
MAGERIT figura en el inventario de métodos de análisis y gestión de riesgos de ENISA.
Productos y servicios complementarios
PILAR es una herramienta que implementa la metodología MAGERIT de análisis y gestión de riesgos, desarrollada por el Centro Criptológico Nacional (CCN) y de amplia utilización en la administración pública española.
es una herramienta que implementa la metodología MAGERIT de análisis y gestión de riesgos, desarrollada por el Centro Criptológico Nacional (CCN) y de amplia utilización en la administración pública española.
Los organismos de la administración pública española pueden solicitar una licencia libre de cargos al Centro Criptológico Nacional; para ello, dirija su solicitud a Centro Criptológico Nacional ccn@cni.es
Objetivos
MAGERIT persigue los siguientes Objetivos Directos:
- Concienciar a los responsables de las organizaciones de información de la existencia de riesgos y de la necesidad de gestionarlos
- Ofrecer un método sistemático para analizar los riesgos derivados del uso de tecnologías de la información y comunicaciones (TIC)
- Ayudar a descubrir y planificar el tratamiento oportuno para mantener los riesgos bajo control Indirectos
- Preparar a la Organización para procesos de evaluación, auditoría, certificación o acreditación, según corresponda en cada caso
Organización de las guías
MAGERIT versión 3 se estructura en tres libros: "Método", "Catálogo de Elementos" y "Guía de Técnicas".
Método
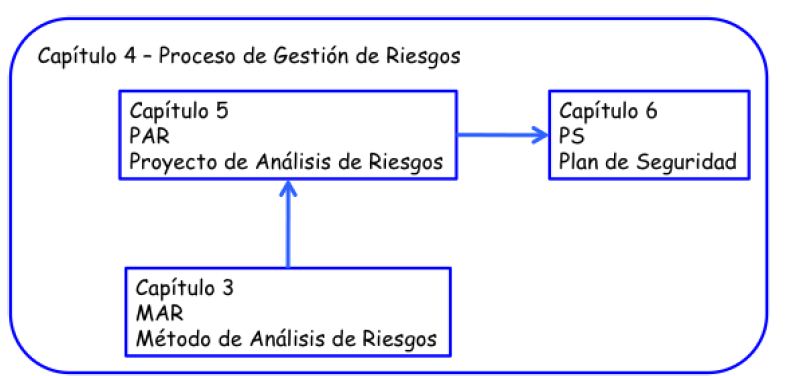
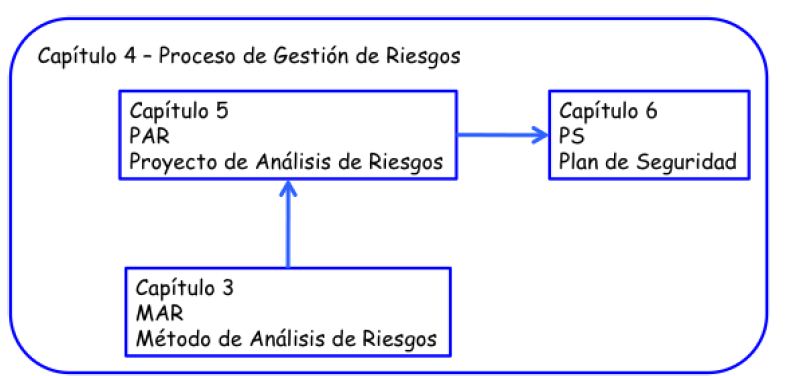
Se estructura de la siguiente forma:
- El capítulo 2 presenta los conceptos informalmente. En particular se enmarcan las actividades de análisis y tratamiento dentro de un proceso integral de gestión de riesgos.
- El capítulo 3 concreta los pasos y formaliza las actividades de análisis de los riesgos.
- El capítulo 4 describe opciones y criterios de tratamiento de los riesgos y formaliza las actividades de gestión de riesgos.
- El capítulo 5 se centra en los proyectos de análisis de riesgos, proyectos en los que nos veremos inmersos para realizar el primer análisis de riesgos de un sistema y eventualmente cuando hay cambios sustanciales y hay que rehacer el modelo ampliamente.
- El capítulo 6 formaliza las actividades de los planes de seguridad, a veces denominados planes directores o planes estratégicos.
- El capítulo 7 se centra en el desarrollo de sistemas de información y cómo el análisis de riesgos sirve para gestionar la seguridad del producto final desde su concepción inicial hasta su puesta en producción, así como a la protección del propio proceso de desarrollo.
- El capítulo 8 se anticipa a algunos problemas que aparecen recurrentemente cuando se realizan análisis de riesgos.
Los apéndices recogen material de consulta:
- Un glosario,
- Referencias bibliográficas consideradas para el desarrollo de esta metodología,
- Referencias al marco legal que encuadra las tareas de análisis y gestión en la Administración Pública Española,
- El marco normativo de evaluación y certificación
- Las características que se requieren de las herramientas, presentes o futuras, para soportar el proceso de análisis y gestión de riesgos,
- Una guía comparativa de cómo Magerit versión 1 ha evolucionado a la versión 2 y a esta versión 3
Catálogo de Elementos
Marca unas pautas en cuanto a:
- Tipos de activos
- Dimensiones de valoración de los activos
- Criterios de valoración de los activos
- Amenazas típicas sobre los sistemas de información
- Salvaguardas a considerar para proteger sistemas de información
Se persiguen dos objetivos:
- Por una parte, facilitar la labor de las personas que acometen el proyecto, en el sentido de ofrecerles elementos estándar a los que puedan adscribirse rápidamente, centrándose en lo específico del sistema objeto del análisis.
- Por otra, homogeneizar los resultados de los análisis, promoviendo una terminología y unos criterios uniformes que permitan comparar e incluso integrar análisis realizados por diferentes equipos.
Cada sección incluye una notación XML que se empleará para publicar regularmente los elementos en un formato estándar capaz de ser procesado automáticamente por herramientas de análisis y gestión.
Si el lector usa una herramienta de análisis y gestión de riesgos, este catálogo será parte de la misma; si el análisis se realiza manualmente, este catálogo proporciona una amplia base de partida para avanzar rápidamente sin distracciones ni olvidos.
Guía de Técnicas
Aporta luz adicional y orientación sobre algunas técnicas que se emplean habitualmente para llevar a cabo proyectos de análisis y gestión de riesgos:
- Técnicas específicas para el análisis de riesgos
- Análisis mediante tablas
- Análisis algorítmico
- Árboles de ataque
- Técnicas generales
- Técnicas gráficas
- Sesiones de trabajo: entrevistas, reuniones y presentaciones
Valoración Delphi Se trata de una guía de consulta. Según el lector avance por la tareas del proyecto, se le recomendará el uso de ciertas técnicas específicas, de las que esta guía busca ser una introducción, así como proporcionar referencias para que el lector profundice en las técnicas presentadas.
Experiencias de aplicación de Magerit
Ejemplo de aplicación de Magerit versión 2 junto con la herramienta PILAR:
Derechos de utilización
MAGERIT es una metodología de carácter público, puede ser utilizada libremente y no requiere autorización previa. En cualquier explotación de la obra se hará constar la autoría original.
Responsable del Producto
Secretaría General de Administración Digital.
![]() Libro II: Catálogo de Elementos (PDF-3,37 MB)
Libro II: Catálogo de Elementos (PDF-3,37 MB)
![]() Libro III: Guía de Técnicas (PDF-1,28 MB)
Libro III: Guía de Técnicas (PDF-1,28 MB)
![]() Book I: Method (PDF-1,44 MB)
Book I: Method (PDF-1,44 MB) 
 Book I: Method (EPUB-2,94 MB)
Book I: Method (EPUB-2,94 MB)
![]() Book II: Catalogue (PDF-270 KB)
Book II: Catalogue (PDF-270 KB)
![]() Book III: Techniques (PDF-157 KB)
Book III: Techniques (PDF-157 KB)